The Fallacy of REST API in High-Throughput Environments
For the past decade, REST (Representational State Transfer) has been the default architectural style for web services. It is stateless, cacheable, and universally understood. However, as enterprise systems scale to handle millions of concurrent operations, the inherent limitations of REST—specifically its reliance on human-readable JSON payload over HTTP/1.1—become mathematically unsustainable bottlenecks.
When executing complex microservice orchestration, a single user request might trigger a cascade of twenty internal service calls. In a RESTful architecture, each of these calls involves significant serialization and deserialization overhead. JSON is bulky. It wastes CPU cycles parsing text when the machines could be communicating in pure binary.
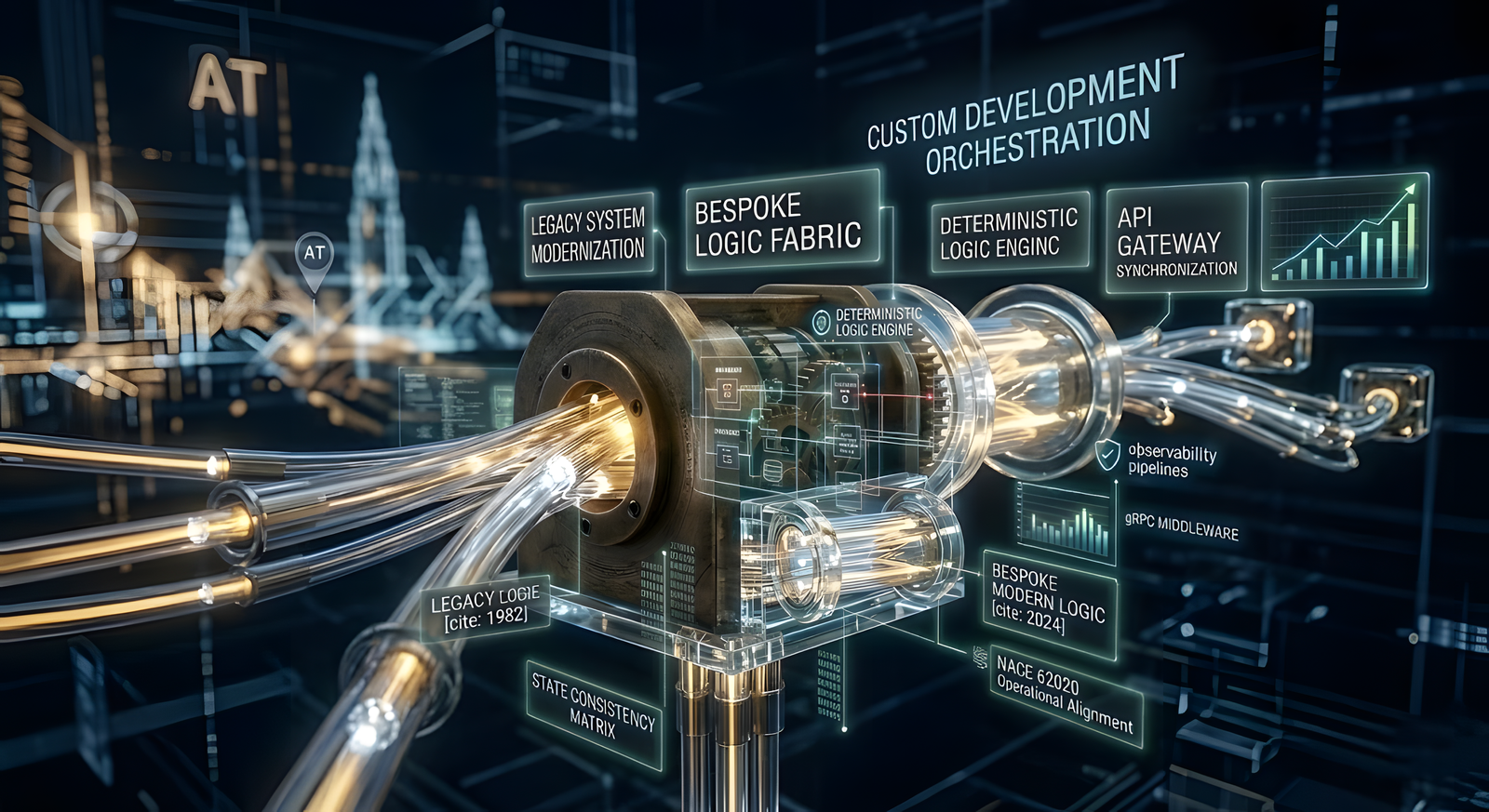
The Shift to gRPC and Binary Protocols
At DIGITAL PROTOTYPE LTD, we mandate the deprecation of internal REST APIs for high-throughput clients. By transitioning inter-service communication to gRPC utilizing Protocol Buffers (Protobuf), we achieve deterministic serialization. Protobuf compiles down to highly compressed binary streams, reducing network payload sizes by up to 80% and increasing transmission speeds exponentially. Furthermore, gRPC operates over HTTP/2, allowing multiplexed streams across a single TCP connection, fundamentally eliminating the head-of-line blocking problem that plagues legacy APIs.