// ENGINEERING DOGMA
Our
Values
We do not subscribe to corporate buzzwords. Our values are uncompromising architectural principles that dictate how we engineer, deploy, and secure enterprise infrastructure.
I. Mathematical Determinism Over Speculation
The technology industry has been poisoned by the mantra of "move fast and break things." In the enterprise sector—where logistics chains, financial clearing, and medical telemetry are at stake—breaking things is not innovation; it is gross negligence.
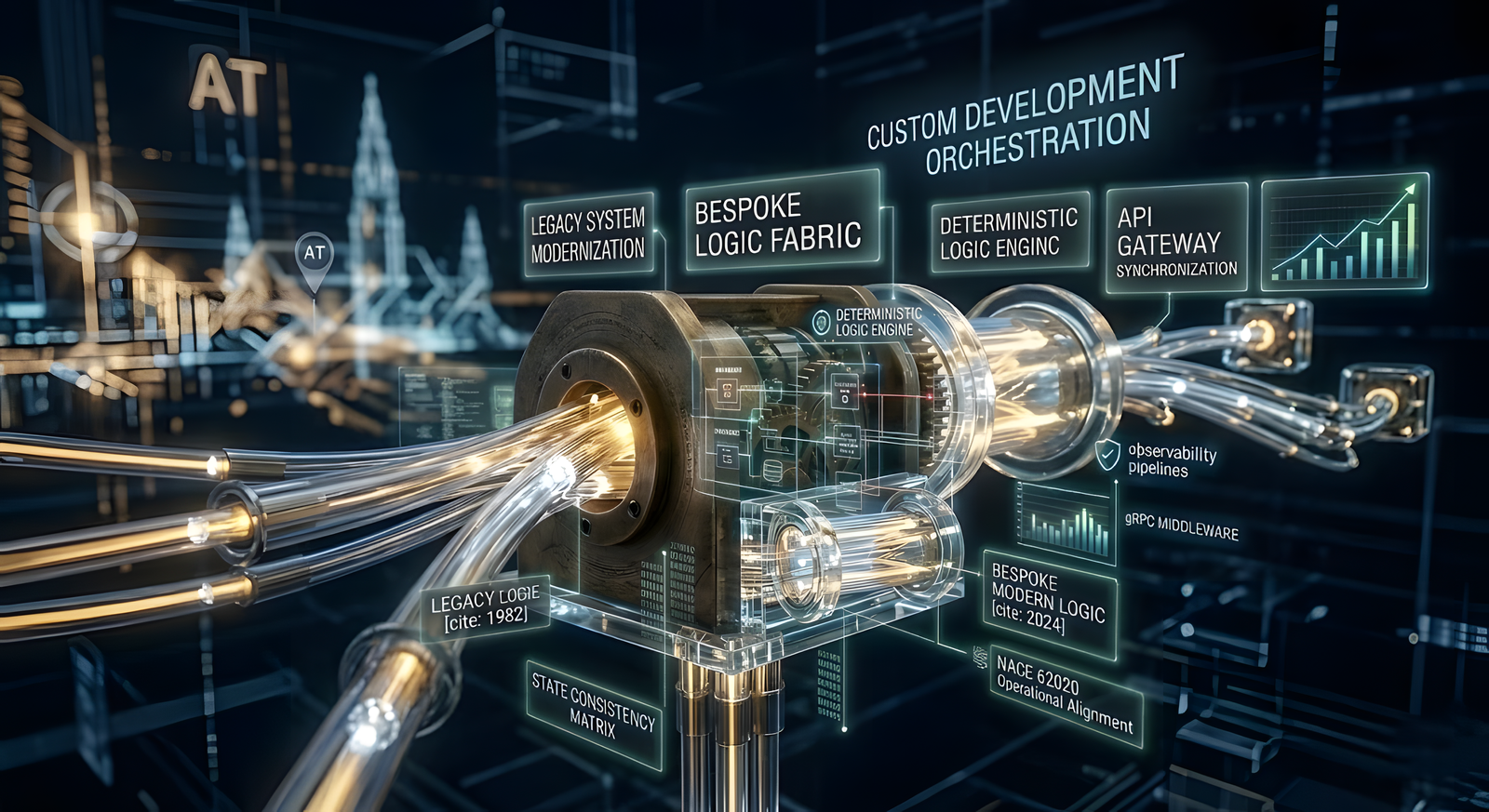
At DIGITAL PROTOTYPE LTD, our foundational value is absolute mathematical determinism. We do not engage in speculative "agile" development where architecture is figured out on the fly. We blueprint the exact state machine before a single line of code is committed. We engineer systems that are completely idempotent—guaranteeing that whether a transaction is processed once or interrupted by a catastrophic server failure and retried ten times, the final state of the database remains flawlessly accurate. We value predictable, mathematically sound execution above all else.
II. Sovereign Control Over Vendor Dependency
For the last decade, corporations have eagerly surrendered their intellectual property and data sovereignty to hyperscale cloud providers and fragmented Software-as-a-Service (SaaS) vendors. This has resulted in exorbitant egress taxes, crippling vendor lock-in, and severe compliance liabilities.
We value absolute Sovereign Control. We believe that an enterprise's proprietary logic and core data must belong entirely to the enterprise. We architect localized infrastructure, repatriate heavy compute workloads to owned bare-metal clusters, and deploy Sovereign AI models that execute entirely within our clients' perimeters. We build systems that free our clients from the arbitrary pricing models and hidden telemetry of third-party vendors.
III. Cryptographic Paranoia as a Standard
Trust is a vulnerability. The traditional concept of a "secure internal network" is an architectural illusion that ransomware syndicates exploit daily. We operate under the assumption that the network is already hostile.
Our value is Cryptographic Paranoia. We enforce Sovereign Perimeter Control across all deployments. Every microservice, every API gateway, and every internal node must mathematically prove its identity via mutual TLS (mTLS) for every single transaction. We do not rely on static passwords or VPNs; we utilize dynamic, time-bound tokens and strict micro-segmentation. If a threat actor breaches an endpoint, our architecture guarantees they encounter a cryptographic dead end, neutralizing lateral movement instantly.
IV. Intellectual Capital Over Headcount
The traditional agency model relies on billing clients for hundreds of junior developers writing fragile, boilerplate code. This brute-force approach inflates budgets and exponentially increases the surface area for security vulnerabilities and technical debt.
We value intense, concentrated intellectual capital. We believe that a small pod of elite, specialized systems architects and cryptographic engineers will consistently outperform a massive army of outsourced coders. By utilizing strict Domain-Driven Design and memory-safe languages like Rust and Go, our tightly controlled engineering units deliver high-throughput, latency-optimized architectures at a fraction of the traditional timeline. We sell unparalleled expertise, not billable hours.
V. The Economics of Architecture
Software engineering is not a sub-department of IT; it is the fundamental economic driver of the modern corporation. A bloated, poorly optimized legacy monolith is not just a technical problem—it is a massive financial liability sitting on the balance sheet, draining OpEx through cloud costs and emergency maintenance.
We value the absolute alignment of code and capital. Every architectural decision we make is run through a strict economic filter. Whether we are strangling a legacy system to reduce server costs by 60%, or implementing an Event-Driven Architecture to ensure zero downtime during market peaks, our ultimate objective is to transform fragile technical debt into a highly optimized, capital-generating digital asset.
Do these principles align with your board?
If your enterprise requires engineering driven by strict determinism and cryptographic security, we invite you to initiate a commercial dialogue.
Initiate Strategy Briefing